
Generally speaking, the pattern is always the same. You will find a vulnerability, you will exploit it, then comes the part of privileges escalation. And that's it, you ...

Generally speaking, the pattern is always the same. You will find a vulnerability, you will exploit it, then comes the part of privileges escalation. And that's it, you ...
Knil.click is a platform that respects the privacy of their users and allows you to encrypt and secure URLs or Qr Codes with a password.

Shodan is a search engine very different from the classic search engines that we are used to. Indeed, when Google or Yahoo! crawl only for ports 80 (http) and 443 (https) ...
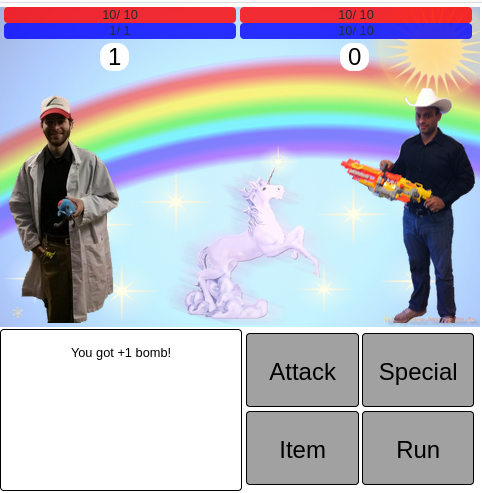
For this challenge as the description tells us, we should “Win an unwinnable game to receive the flag!” And it also says, “The developer has left in some bugs!”
2021/06/12 -
CTF
,
Reverse Engineering
For this challenge we can download a compiled C file called "crackme2_1.out". When I execute the file, a simple addition of 3 numbers, randomly generate, is required to ...